About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
Apple security documents reference vulnerabilities by CVE-ID when possible.
For more information about security, see the Apple Product Security page.

macOS Mojave 10.14.4, Security Update 2019-002 High Sierra, Security Update 2019-002 Sierra
Released March 25, 2019
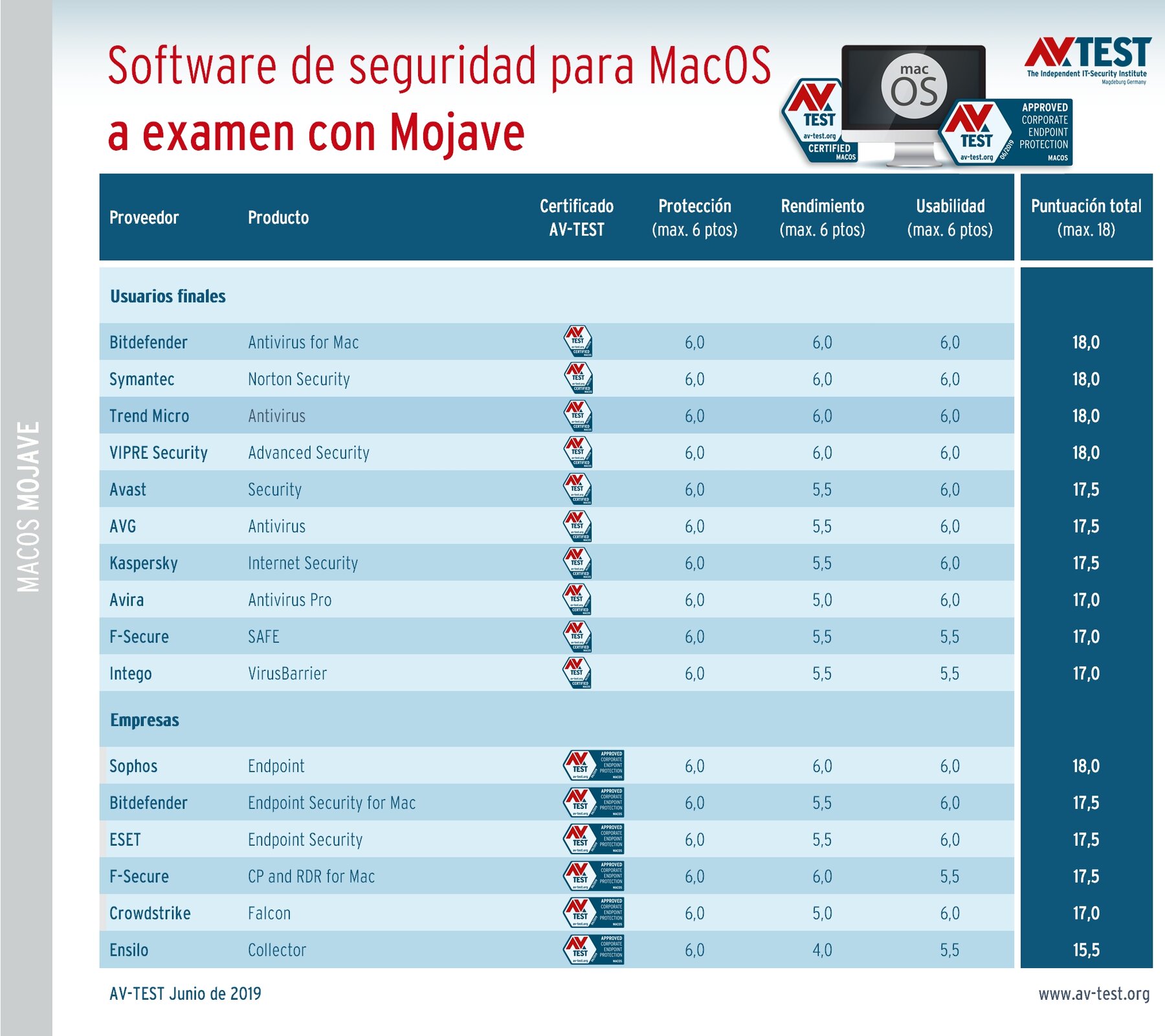
.signed by “Trend Micro, Inc.” which will be incompatible with a future version of macOS. Contact the developer for support. I get this message on mac with latest system updates:Existing software on your system loaded a system extension signed by “Trend Micro, Inc.” which wi. Antivirus for Mac - Protection 1 Mac 147812400 $39.95 $ Antivirus for Mac - Protection 1 Mac tmamer.
802.1X
Available for: macOS Mojave 10.14.3
Impact: An attacker in a privileged network position may be able to intercept network traffic
Description: A logic issue was addressed with improved state management.
CVE-2019-6203: Dominic White of SensePost (@singe)
Entry added April 15, 2019
802.1X
Available for: macOS High Sierra 10.13.6
Impact: An untrusted radius server certificate may be trusted
Description: A validation issue existed in Trust Anchor Management. This issue was addressed with improved validation.
CVE-2019-8531: an anonymous researcher, QA team of SecureW2
Entry added May 15, 2019
Accounts
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted vcf file may lead to a denial of service
Description: A denial of service issue was addressed with improved validation.
CVE-2019-8538: Trevor Spiniolas (@TrevorSpiniolas)
Entry added April 3, 2019
APFS
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: A logic issue existed resulting in memory corruption. This was addressed with improved state management.
CVE-2019-8534: Mac working with Trend Micro's Zero Day Initiative
Entry added April 15, 2019
AppleGraphicsControl
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow was addressed with improved size validation.
CVE-2019-8555: Zhiyi Zhang of 360 ESG Codesafe Team, Zhuo Liang and shrek_wzw of Qihoo 360 Nirvan Team
Bom
Available for: macOS Mojave 10.14.3
Impact: A malicious application may bypass Gatekeeper checks
Description: This issue was addressed with improved handling of file metadata.
CVE-2019-6239: Ian Moorhouse and Michael Trimm
CFString
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted string may lead to a denial of service
Description: A validation issue was addressed with improved logic.
CVE-2019-8516: SWIPS Team of Frifee Inc.
configd
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8552: Mohamed Ghannam (@_simo36)
Contacts
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2019-8511: an anonymous researcher
CoreCrypto
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2019-8542: an anonymous researcher
DiskArbitration
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: An encrypted volume may be unmounted and remounted by a different user without prompting for the password
Description: A logic issue was addressed with improved state management.
CVE-2019-8522: Colin Meginnis (@falc420)
FaceTime
Available for: macOS Mojave 10.14.3
Impact: A user’s video may not be paused in a FaceTime call if they exit the FaceTime app while the call is ringing
Description: An issue existed in the pausing of FaceTime video. The issue was resolved with improved logic.
CVE-2019-8550: Lauren Guzniczak of Keystone Academy
FaceTime
Available for: macOS Mojave 10.14.3
Impact: A local attacker may be able to view contacts from the lock screen
Description: A lock screen issue allowed access to contacts on a locked device. This issue was addressed with improved state management.
CVE-2019-8777: Abdullah H. AlJaber (@aljaber) of AJ.SA
Entry added October 8, 2019
Feedback Assistant
Trend Micro For Mac Review
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to gain root privileges
Description: A race condition was addressed with additional validation.
CVE-2019-8565: CodeColorist of Ant-Financial LightYear Labs
Feedback Assistant
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to overwrite arbitrary files
Description: This issue was addressed with improved checks.
CVE-2019-8521: CodeColorist of Ant-Financial LightYear Labs
file
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted file might disclose user information
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8906: Francisco Alonso
Entry updated April 15, 2019
Graphics Drivers
Available for: macOS Mojave 10.14.3
Impact: An application may be able to read restricted memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8519: Aleksandr Tarasikov (@astarasikov), Juwei Lin (@panicaII) and Junzhi Lu of Trend Micro Research working with Trend Micro's Zero Day Initiative, Lilang Wu and Moony Li of Trend Micro
Entry updated August 1, 2019
iAP
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2019-8542: an anonymous researcher
IOGraphics
Available for: macOS Mojave 10.14.3
Impact: A Mac may not lock when disconnecting from an external monitor
Description: A lock handling issue was addressed with improved lock handling.
CVE-2019-8533: an anonymous researcher, James Eagan of Télécom ParisTech, R. Scott Kemp of MIT, and Romke van Dijk of Z-CERT
IOHIDFamily
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to cause unexpected system termination or read kernel memory
Description: A memory corruption issue was addressed with improved state management.
CVE-2019-8545: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
IOKit
Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A local user may be able to read kernel memory
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8504: an anonymous researcher
IOKit SCSI
Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved input validation.
CVE-2019-8529: Juwei Lin (@panicaII) of Trend Micro Research working with Trend Micro's Zero Day Initiative
Entry updated April 15, 2019
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: A local user may be able to read kernel memory
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2018-4448: Brandon Azad
Entry added September 17, 2019
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A remote attacker may be able to alter network traffic data
Description: A memory corruption issue existed in the handling of IPv6 packets. This issue was addressed with improved memory management.
CVE-2019-5608: Apple
Entry added August 6, 2019
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A remote attacker may be able to cause unexpected system termination or corrupt kernel memory
Description: A buffer overflow was addressed with improved size validation.
CVE-2019-8527: Ned Williamson of Google and derrek (@derrekr6)
Kernel
Available for: macOS Mojave 10.14.3, macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A use after free issue was addressed with improved memory management.
CVE-2019-8528: Fabiano Anemone (@anoane), Zhao Qixun (@S0rryMybad) of Qihoo 360 Vulcan Team
Entry added April 3, 2019, updated August 1, 2019
Kernel
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
Impact: Mounting a maliciously crafted NFS network share may lead to arbitrary code execution with system privileges
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2019-8508: Dr. Silvio Cesare of InfoSect
Kernel
Available for: macOS Mojave 10.14.3
Impact: An application may be able to gain elevated privileges
Description: A logic issue was addressed with improved state management.
CVE-2019-8514: Samuel Groß of Google Project Zero
Kernel
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to determine kernel memory layout
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8540: Weibo Wang (@ma1fan) of Qihoo 360 Nirvan Team
Kernel
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to read kernel memory
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-7293: Ned Williamson of Google
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to determine kernel memory layout
Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
CVE-2019-6207: Weibo Wang of Qihoo 360 Nirvan Team (@ma1fan)
CVE-2019-8510: Stefan Esser of Antid0te UG
Kernel
Available for: macOS Mojave 10.14.3
Impact: A remote attacker may be able to leak memory
Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
CVE-2019-8547: derrek (@derrekr6)
Entry added August 1, 2019
Kernel
Available for: macOS Mojave 10.14.3
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved state management.
CVE-2019-8525: Zhuo Liang and shrek_wzw of Qihoo 360 Nirvan Team
Entry added August 1, 2019
libmalloc
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: A malicious application may be able to modify protected parts of the file system
Description: A configuration issue was addressed with additional restrictions.
CVE-2018-4433: Vitaly Cheptsov
Entry added August 1, 2019, updated September 17, 2019
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted mail message may lead to S/MIME signature spoofing
Description: An issue existed in the handling of S-MIME certificates. This issue was addressed with improved validation of S-MIME certificates.
CVE-2019-8642: Maya Sigal of Freie Universität Berlin and Volker Roth of Freie Universität Berlin
Entry added August 1, 2019
Available for: macOS Mojave 10.14.3
Impact: An attacker in a privileged network position may be able to intercept the contents of S/MIME-encrypted e-mail
Description: An issue existed in the handling of encrypted Mail. This issue was addressed with improved isolation of MIME in Mail.
CVE-2019-8645: Maya Sigal of Freie Universität Berlin and Volker Roth of Freie Universität Berlin
Entry added August 1, 2019
Messages
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to view sensitive user information
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2019-8546: ChiYuan Chang
Modem CCL
Available for: macOS Mojave 10.14.3
Impact: An application may be able to gain elevated privileges
Description: An input validation issue was addressed with improved memory handling.
CVE-2019-8579: an anonymous researcher
Entry added April 15, 2019
Notes
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to view a user’s locked notes
Description: An access issue was addressed with improved memory management.
CVE-2019-8537: Greg Walker (gregwalker.us)
PackageKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A logic issue was addressed with improved validation.
CVE-2019-8561: Jaron Bradley of Crowdstrike
Perl
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: Multiple issues in Perl
Description: Multiple issues in Perl were addressed in this update.
CVE-2018-12015: Jakub Wilk
CVE-2018-18311: Jayakrishna Menon
CVE-2018-18313: Eiichi Tsukata
Power Management
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: Multiple input validation issues existed in MIG generated code. These issues were addressed with improved validation.
CVE-2019-8549: Mohamed Ghannam (@_simo36) of SSD Secure Disclosure (ssd-disclosure.com)
QuartzCore
Available for: macOS Mojave 10.14.3
Impact: Processing malicious data may lead to unexpected application termination
Description: Multiple memory corruption issues were addressed with improved input validation.
Trend Micro Security For Mac
CVE-2019-8507: Kai Lu of Fortinet's FortiGuard Labs
Sandbox
Available for: macOS Mojave 10.14.3
Impact: A sandboxed process may be able to circumvent sandbox restrictions
Description: A logic issue was addressed with improved restrictions.
CVE-2019-8618: Brandon Azad
Entry added August 1, 2019
Security
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: An application may be able to gain elevated privileges
Description: A use after free issue was addressed with improved memory management.
CVE-2019-8526: Linus Henze (pinauten.de)
Security
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to read restricted memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8520: Antonio Groza, The UK's National Cyber Security Centre (NCSC)
Security
Available for: macOS Mojave 10.14.3
Impact: An untrusted radius server certificate may be trusted
Description: A validation issue existed in Trust Anchor Management. This issue was addressed with improved validation.
CVE-2019-8531: an anonymous researcher, QA team of SecureW2
Security
Available for: macOS Mojave 10.14.3
Impact: An untrusted radius server certificate may be trusted
Description: A validation issue existed in Trust Anchor Management. This issue was addressed with improved validation.
CVE-2019-8531: an anonymous researcher, QA team of SecureW2
Entry added May 15, 2019
Siri
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to initiate a Dictation request without user authorization
Description: An API issue existed in the handling of dictation requests. This issue was addressed with improved validation.
CVE-2019-8502: Luke Deshotels of North Carolina State University, Jordan Beichler of North Carolina State University, William Enck of North Carolina State University, Costin Carabaș of University POLITEHNICA of Bucharest, and Răzvan Deaconescu of University POLITEHNICA of Bucharest
Time Machine
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A local user may be able to execute arbitrary shell commands
Description: This issue was addressed with improved checks.
CVE-2019-8513: CodeColorist of Ant-Financial LightYear Labs
Touch Bar Support
Available for: macOS Mojave 10.14.3
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8569: Viktor Oreshkin (@stek29)
Entry added August 1, 2019
TrueTypeScaler
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8517: riusksk of VulWar Corp working with Trend Micro Zero Day Initiative
Wi-Fi
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: An attacker in a privileged network position can modify driver state
Description: A logic issue was addressed with improved validation.
CVE-2019-8564: Hugues Anguelkov during an internship at Quarkslab
Entry added April 15, 2019
Wi-Fi
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: An attacker in a privileged network position can modify driver state
Description: A logic issue was addressed with improved state management.
CVE-2019-8612: Milan Stute of Secure Mobile Networking Lab at Technische Universität Darmstadt
Entry added August 1, 2019
Wi-Fi
Available for: macOS Mojave 10.14.3
Impact: A device may be passively tracked by its WiFi MAC address
Description: A user privacy issue was addressed by removing the broadcast MAC address.
CVE-2019-8567: David Kreitschmann and Milan Stute of Secure Mobile Networking Lab at Technische Universität Darmstadt
Entry added August 1, 2019
xar
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted package may lead to arbitrary code execution
Description: A validation issue existed in the handling of symlinks. This issue was addressed with improved validation of symlinks.
CVE-2019-6238: Yiğit Can YILMAZ (@yilmazcanyigit)
Entry added April 15, 2019
XPC
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to overwrite arbitrary files
Description: This issue was addressed with improved checks.
CVE-2019-8530: CodeColorist of Ant-Financial LightYear Labs
Additional recognition
Accounts
We would like to acknowledge Milan Stute of Secure Mobile Networking Lab at Technische Universität Darmstadt for their assistance.
Books
We would like to acknowledge Yiğit Can YILMAZ (@yilmazcanyigit) for their assistance.
Kernel
We would like to acknowledge Brandon Azad, Brandon Azad of Google Project Zero, Daniel Roethlisberger of Swisscom CSIRT, Raz Mashat (@RazMashat) of Ilan Ramon High School for their assistance.
Entry updated September 17, 2019
We would like to acknowledge Craig Young of Tripwire VERT and Hanno Böck for their assistance.
Time Machine
We would like to acknowledge CodeColorist of Ant-Financial LightYear Labs for their assistance.
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
Apple security documents reference vulnerabilities by CVE-ID when possible.
For more information about security, see the Apple Product Security page.
macOS Mojave 10.14.6, Security Update 2019-004 High Sierra, Security Update 2019-004 Sierra
Released July 22, 2019
AppleGraphicsControl
Available for: macOS Mojave 10.14.5
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2019-8693: Arash Tohidi of Solita
autofs
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: Extracting a zip file containing a symbolic link to an endpoint in an NFS mount that is attacker controlled may bypass Gatekeeper
Description: This was addressed with additional checks by Gatekeeper on files mounted through a network share.
CVE-2019-8656: Filippo Cavallarin
Bluetooth
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2018-19860
Bluetooth
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: An attacker in a privileged network position may be able to intercept Bluetooth traffic (Key Negotiation of Bluetooth - KNOB)
Description: An input validation issue existed in Bluetooth. This issue was addressed with improved input validation.
CVE-2019-9506: Daniele Antonioli of SUTD, Singapore, Dr. Nils Ole Tippenhauer of CISPA, Germany, and Prof. Kasper Rasmussen of University of Oxford, England
The changes for this issue mitigate CVE-2020-10135.
Entry added August 13, 2019, updated June 25, 2020
Carbon Core
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause arbitrary code execution
Description: A use after free issue was addressed with improved memory management.
CVE-2019-8661: Natalie Silvanovich of Google Project Zero
Core Data
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to leak memory
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8646: Natalie Silvanovich of Google Project Zero
Trend Micro For Mac Mojave 2017
Core Data
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause unexpected application termination or arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2019-8660: Samuel Groß and Natalie Silvanovich of Google Project Zero
CUPS
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: An attacker in a privileged network position may be able to execute arbitrary code
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2019-8675: Stephan Zeisberg (github.com/stze) of Security Research Labs (srlabs.de)
CVE-2019-8696: Stephan Zeisberg (github.com/stze) of Security Research Labs (srlabs.de)
Entry added August 14, 2019, updated September 17, 2019
Disk Management
Available for: macOS Mojave 10.14.5
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8539: ccpwd working with Trend Micro's Zero Day Initiative
Entry added September 17, 2019
Disk Management
Available for: macOS Mojave 10.14.5
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8697: ccpwd working with Trend Micro’s Zero Day Initiative
FaceTime
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2019-8648: Tao Huang and Tielei Wang of Team Pangu
Found in Apps
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to leak memory
Description: This issue was addressed with improved checks.
CVE-2019-8663: Natalie Silvanovich of Google Project Zero
Game Center
Available for: macOS Mojave 10.14.5
Impact: A local user may be able to read a persistent account identifier
Description: This issue was addressed with a new entitlement.
CVE-2019-8702: Min (Spark) Zheng and Xiaolong Bai of Alibaba Inc.
Entry added February 24, 2020
Grapher
Available for: macOS Mojave 10.14.5
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8695: riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative
Graphics Drivers
Available for: macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2019-8691: Aleksandr Tarasikov (@astarasikov), Arash Tohidi of Solita, Lilang Wu and Moony Li of Trend Micro's Mobile Security Research Team working with Trend Micro's Zero Day Initiative
CVE-2019-8692: Lilang Wu and Moony Li of Trend Micro Mobile Security Research Team working with Trend Micro's Zero Day Initiative
Entry updated July 25, 2019
Heimdal
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: An issue existed in Samba that may allow attackers to perform unauthorized actions by intercepting communications between services
Description: This issue was addressed with improved checks to prevent unauthorized actions.
CVE-2018-16860: Isaac Boukris and Andrew Bartlett of the Samba Team and Catalyst
IOAcceleratorFamily
Available for: macOS Mojave 10.14.5
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8694: Arash Tohidi of Solita
libxslt
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: A remote attacker may be able to view sensitive information
Description: A stack overflow was addressed with improved input validation.
CVE-2019-13118: found by OSS-Fuzz
Quick Look
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: An attacker may be able to trigger a use-after-free in an application deserializing an untrusted NSDictionary
Description: This issue was addressed with improved checks.
CVE-2019-8662: Natalie Silvanovich and Samuel Groß of Google Project Zero
Safari
Available for: macOS Mojave 10.14.5
Impact: Visiting a malicious website may lead to address bar spoofing
Description: An inconsistent user interface issue was addressed with improved state management.
CVE-2019-8670: Tsubasa FUJII (@reinforchu)
Security
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8697: ccpwd working with Trend Micro’s Zero Day Initiative
sips
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8701: Simon Huang(@HuangShaomang), Rong Fan(@fanrong1992) and pjf of IceSword Lab of Qihoo 360
Entry added October 8, 2019
Siri
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to leak memory
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8646: Natalie Silvanovich of Google Project Zero
Time Machine
Available for: macOS Mojave 10.14.5
Impact: The encryption status of a Time Machine backup may be incorrect
Description: An inconsistent user interface issue was addressed with improved state management.
CVE-2019-8667: Roland Kletzing of cyber:con GmbH
UIFoundation
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: Parsing a maliciously crafted office document may lead to an unexpected application termination or arbitrary code execution
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8657: riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of document loads. This issue was addressed with improved state management.
CVE-2019-8690: Sergei Glazunov of Google Project Zero
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of synchronous page loads. This issue was addressed with improved state management.
CVE-2019-8649: Sergei Glazunov of Google Project Zero
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue was addressed with improved state management.
CVE-2019-8658: akayn working with Trend Micro's Zero Day Initiative
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2019-8644: G. Geshev working with Trend Micro's Zero Day Initiative
CVE-2019-8666: Zongming Wang (王宗明) and Zhe Jin (金哲) from Chengdu Security Response Center of Qihoo 360 Technology Co. Ltd.
CVE-2019-8669: akayn working with Trend Micro's Zero Day Initiative
CVE-2019-8671: Apple
CVE-2019-8672: Samuel Groß of Google Project Zero
CVE-2019-8673: Soyeon Park and Wen Xu of SSLab at Georgia Tech
CVE-2019-8676: Soyeon Park and Wen Xu of SSLab at Georgia Tech
CVE-2019-8677: Jihui Lu of Tencent KeenLab
CVE-2019-8678: an anonymous researcher, Anthony Lai (@darkfloyd1014) of Knownsec, Ken Wong (@wwkenwong) of VXRL, Jeonghoon Shin (@singi21a) of Theori, Johnny Yu (@straight_blast) of VX Browser Exploitation Group, Chris Chan (@dr4g0nfl4me) of VX Browser Exploitation Group, Phil Mok (@shadyhamsters) of VX Browser Exploitation Group, Alan Ho (@alan_h0) of Knownsec, Byron Wai of VX Browser Exploitation
CVE-2019-8679: Jihui Lu of Tencent KeenLab
CVE-2019-8680: Jihui Lu of Tencent KeenLab
CVE-2019-8681: G. Geshev working with Trend Micro Zero Day Initiative
CVE-2019-8683: lokihardt of Google Project Zero
CVE-2019-8684: lokihardt of Google Project Zero
CVE-2019-8685: akayn, Dongzhuo Zhao working with ADLab of Venustech, Ken Wong (@wwkenwong) of VXRL, Anthony Lai (@darkfloyd1014) of VXRL, and Eric Lung (@Khlung1) of VXRL
CVE-2019-8686: G. Geshev working with Trend Micro's Zero Day Initiative
CVE-2019-8687: Apple
CVE-2019-8688: Insu Yun of SSLab at Georgia Tech
CVE-2019-8689: lokihardt of Google Project Zero
Additional recognition
Classroom
We would like to acknowledge Jeff Johnson of underpassapp.com for their assistance.
Game Center
We would like to acknowledge Min (Spark) Zheng and Xiaolong Bai of Alibaba Inc. for their assistance.